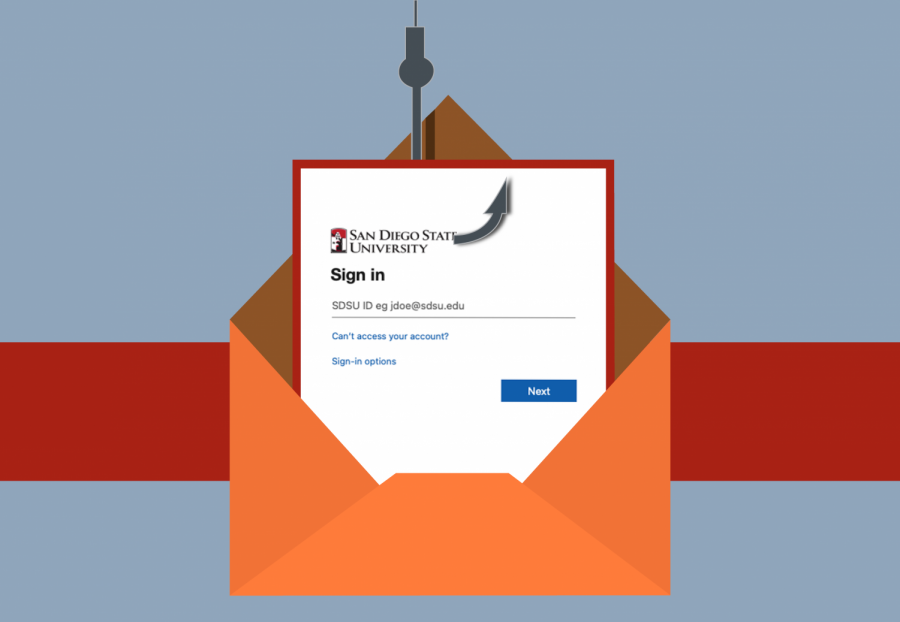
After a significant increase in phishing emails, San Diego State’s IT team is adding an extra step for student log in.
In order to increase security, the team is implementing two-factor authentication for anyone logging into SDSU Google Suite accounts.
By March 5, students, faculty and staff will be required to enroll in Duo, an app that will require a second device to confirm that the correct user is signing in.
Since SDSU switched to an online platform last March, there has been an average of 238 phishing attacks reported every month according to Jerry Sheehan, SDSU’s chief information officer.
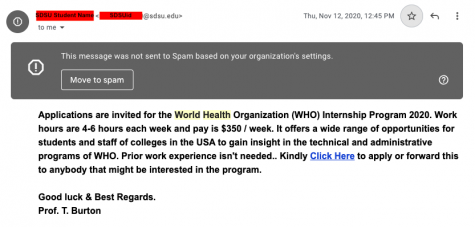
The phishing emails typically consist of financial scams, such as a job or internship opportunity, paycheck updates, or free gift cards, all of which offer large pay and flexibility.
Those who respond to the scams and provide information are at risk of losing access to their identities, bank accounts, or other personal emails/online accounts. The attackers may also be able to access campus systems and retrieve data.
The emails are sent from SDSU accounts, making the offer seem more legitimate. However, Sheehan said that it is not students or alumni sending these false emails.
“Some students will use their SDSU identity to log into other systems like Facebook, or Instagram, and if any of those third-party systems are breached it’s a risk,” Sheehan said.
Once attackers get access to an SDSU email, they are able to see other contacts and send phishing emails to them. Some students are likely to trust these emails if they are from someone they may know.
“If it looks like it’s coming from (SDSU), you can look up that person and they might be a graduate teaching assistant, or faculty member, or a student who you might know,” Sheehan said. “Those are all the ways that they socially hijack our trust.”
Interim Chief Information Security Officer, Ricardo Fitipaldi recommended that students only use their SDSUid for university purposes.
“All it takes is one person to give out their email,” Fitipaldi said. “Once they are in the system, then they can start searching for all the other emails and make a collection that way.”
Duo will enhance security by providing a six-digit code that will be required every time a student or faculty member wants to sign into their SDSUid. A new code will be required for every session, which typically lasts 24 hours, according to Fitipaldi.
The code can be provided through the Duo app, or users can opt to receive it through text or phone call. The app will also send international phone calls and texts for students who are not in the United States due to travel restrictions.
The app will eventually be adopted across all California State University campuses to enhance security for the system.
Anyone who is not enrolled by March 5 will lose access to their SDSU Google Suite.
To enroll in SDSU Duo, download the app with your preferred second device. Learn how to enable your Google Suite at IT’s Security page.
Students, faculty and staff who have received phishing emails can forward them to fraud@sdsu.edu.